TryHackMe — Jr Penetration Tester | Privilege Escalation | Linux Privesc | Part 2 | by Aditya Sharma | Medium

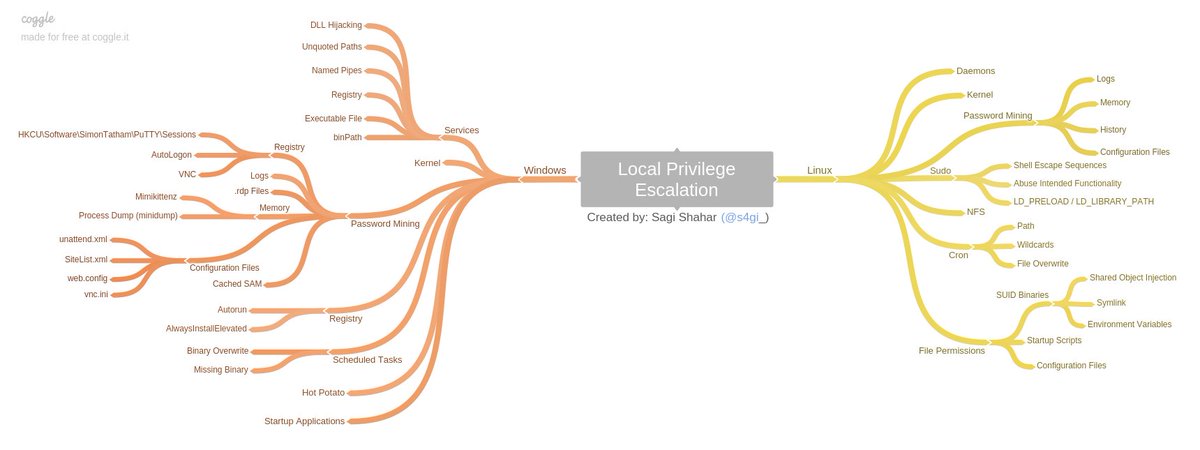
Hacking Articles on X: "Linux privilege Escalation Credit @xtremepentest #infosec #cybersecurity #pentesting #redteam #informationsecurity #CyberSec #networking #networksecurity #infosecurity #cyberattacks #security #linux #cybersecurityawareness ...
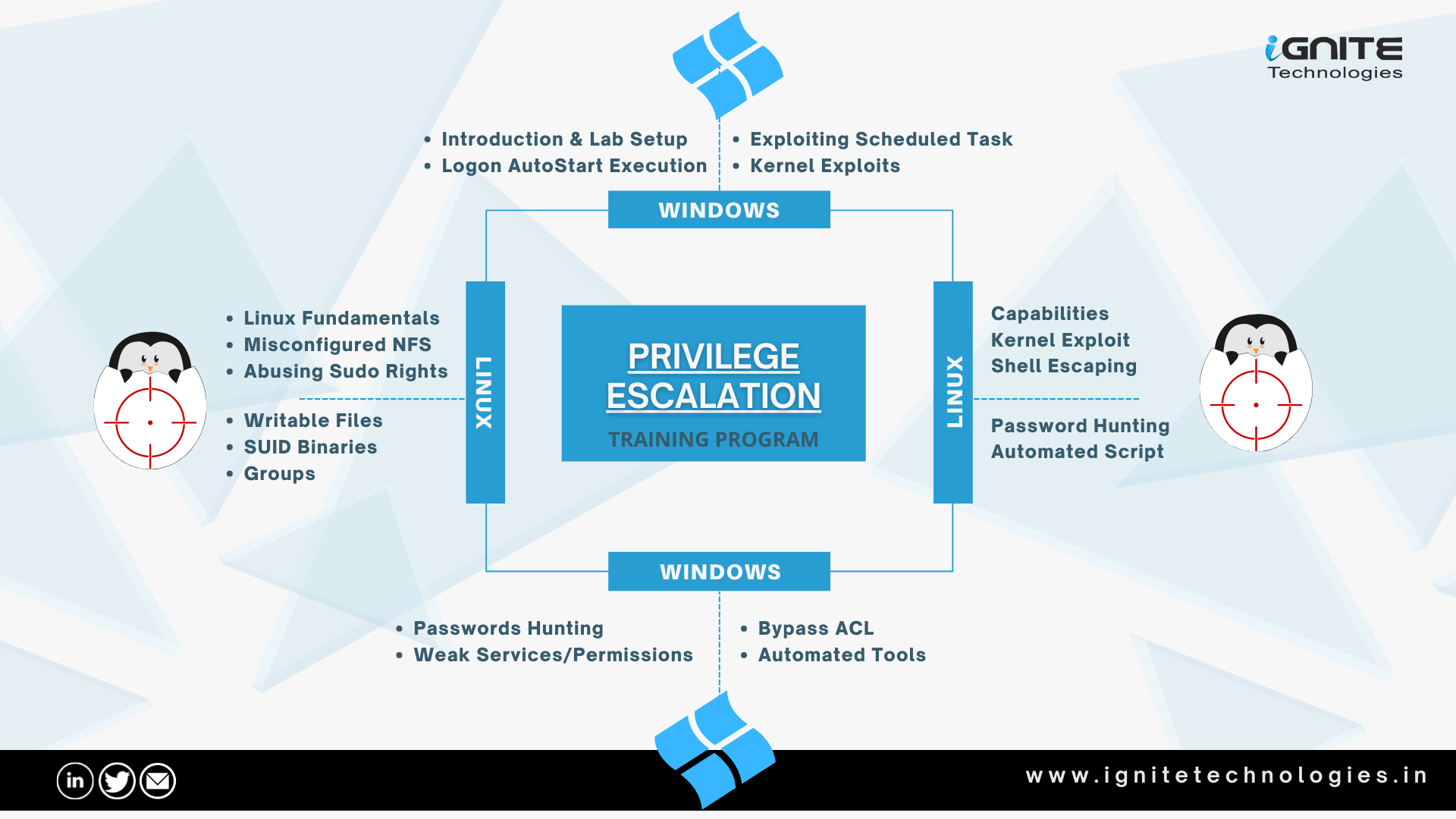
GitHub - Ignitetechnologies/Linux-Privilege-Escalation: This cheatsheet is aimed at the OSCP aspirants to help them understand the various methods of Escalating Privilege on Linux based Machines and CTFs with examples.

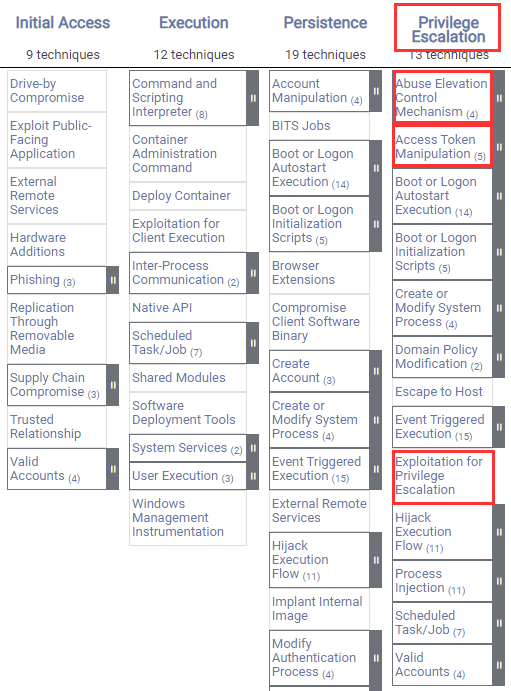
Offensive Security Tool: PEASS (Privilege Escalation Awesome Scripts Suite) As Shell is the beginning, once a hacker accesses a system, which is not so... | By Black Hat Ethical HackingFacebook
![Linux Privilege Escalation - Automated Tools [HINDI] | Part_02 | PentestHint | LinPeas Tutorial - YouTube Linux Privilege Escalation - Automated Tools [HINDI] | Part_02 | PentestHint | LinPeas Tutorial - YouTube](https://i.ytimg.com/vi/p-MoSi5WvIM/mqdefault.jpg)
Linux Privilege Escalation - Automated Tools [HINDI] | Part_02 | PentestHint | LinPeas Tutorial - YouTube

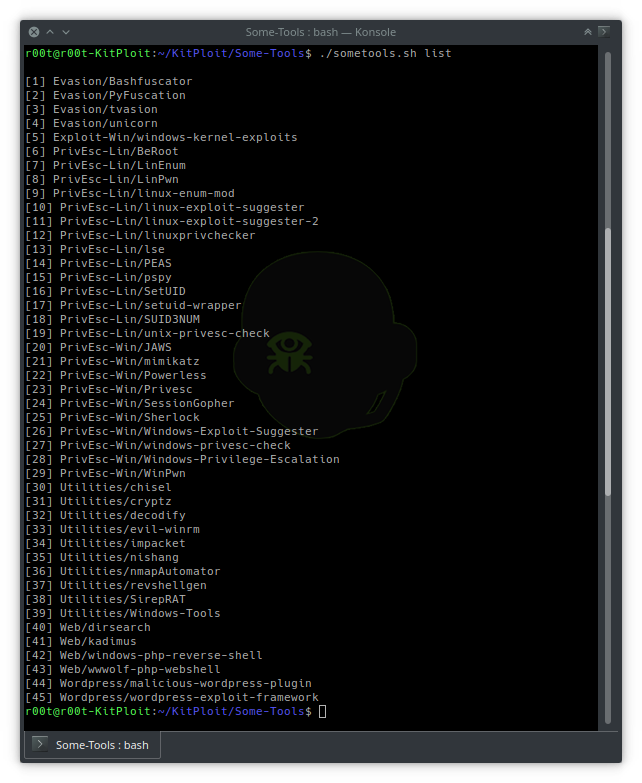
Hacking Articles on X: "Privilege Escalation Tools #infosec #cybersecurity #pentesting #redteam #informationsecurity #CyberSec #networking #networksecurity #infosecurity #cyberattacks #security #linux #cybersecurityawareness #bugbounty #bugbountytips ...

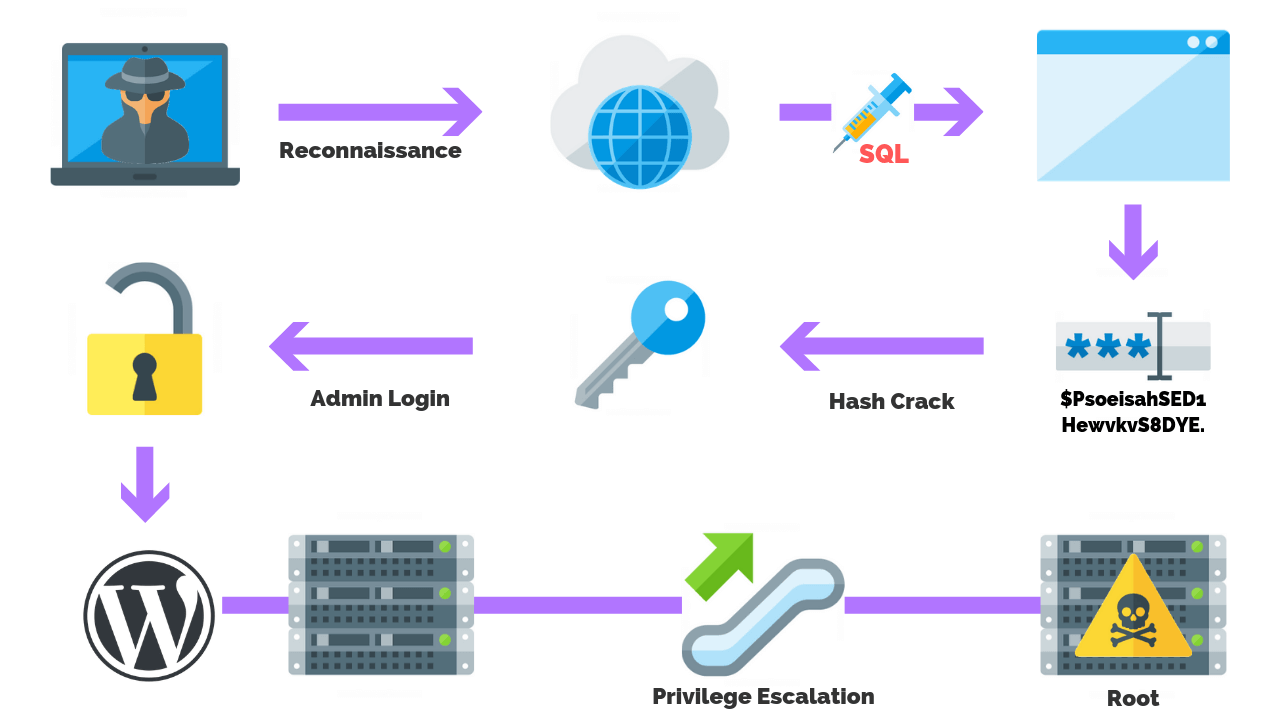
THE CYBER GUY on Instagram: "Linux privilege escalation is the process of exploiting a vulnerability in a Linux system to gain access to privileges that are not normally available to a user.

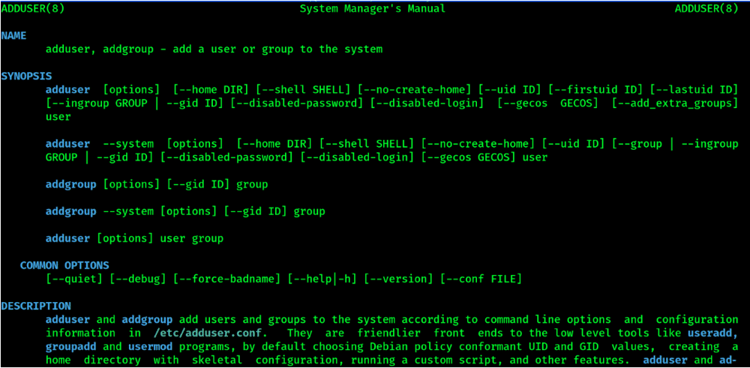

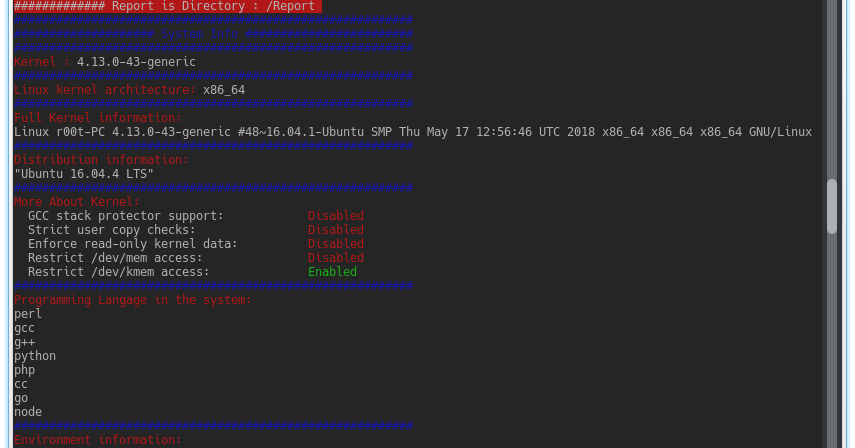
![Linux privilege checker - Advanced Infrastructure Penetration Testing [Book] Linux privilege checker - Advanced Infrastructure Penetration Testing [Book]](https://www.oreilly.com/api/v2/epubs/9781788624480/files/assets/0f21b2d6-ffb5-4181-b736-fc9d36a554da.png)